In September 2021, graduates were once again able to celebrate their hard-fought achievement of earning their undergraduate degree certificate with in person graduation ceremonies on the Plymouth Hoe. Following that in December 2021, postgraduate students from Plymouth were also celebrating their successes with in-person ceremonies at the Plymouth Guild Hall.

These events marked the first return to in person ceremonies since Plymouth Gazette reported on the decision to hold digital celebrations in lieu of traditional ceremonies, which was part of response measures to the Coronavirus pandemic. Both forms of graduation are typically however followed by celebratory social media posts.
It’s not unusual to see photos of graduates with their course-mates and their families popping up on social media followed by numerous congratulatory responses. Indeed – why shouldn’t you post photos of your achievement?
Well, if your post includes a copy of your digital award (usually supplied in PDF format) or a selfie with your newest qualification, you might want to think twice about exactly what you do share to social media.
A quick scroll through social media feeds back in September of 2021 showcased the degree certificates of other graduates from across various different cohorts at Plymouth as well as graduates from other Universities. A similar look around social media now and you can easily find postgraduate transcripts with a variety of sensitive personal data on them.
What the experts are saying about posting your degree certificate online

JISC, which provides the University of Plymouth with a lot of the backbone for its digital infrastructure, warned back in August of 2020, that sharing images of your important documents online can give fraudsters access to information that enables them to make fake documents.
Prospects, which is run by JISC, further explained that sharing your degree certificate online gives fraudsters “access to logos, crests, signatories, stamps, holograms and wording,” further highlighting that these tend to be unique to each higher education institution and are often changed each year to help combat degree fraud.
The Guardian reported on these same sentiments back in June 2018 where they quoted Jayne Rowley, now executive director of student services at JISC, as suggesting that posting your degree certificate online is comparable to sharing a photo of your passport or driving license on the internet.
Social engineering
Aside from your University potentially suffering from degree fraud because of degree certificates or transcripts appearing on social media, the reason you should be concerned is the threat of social engineering.
Social engineering is a broad term that covers a range of manipulation techniques employed by cyber criminals to illicitly gain access to or control over your data. For a keen fraudster looking to gather information about someone or an organization to target, social media provides a fertile ground of intel that can be used as a starting point for a wider campaign of attack.
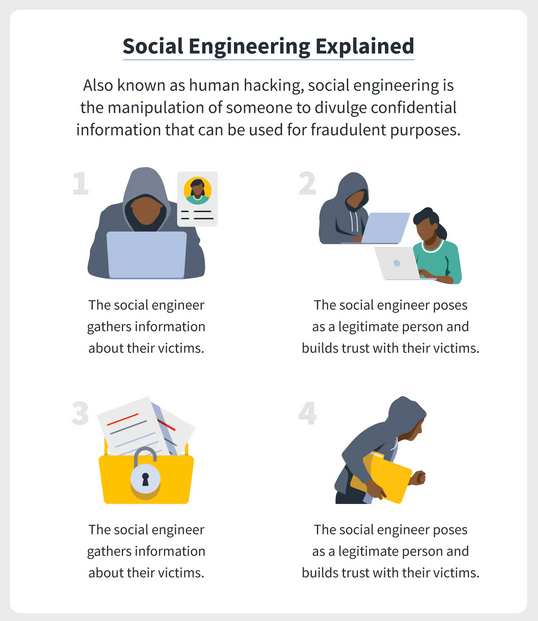
NortonLifeLock (formerly Symantec Corporation), outline that at the core of social engineering is typically a four step process of building false trust with a victim and then using persuasion to gain further information about you and their target.
Being manipulated
As an example, your university statement of results includes your student ID number, your name and your date of birth. If you post this publicly online, you’re giving public access to your date of birth and student id number, which are key components in how whichever university you are enrolled at knows who you are.
In a scenario where an attacker wants to gather further information about you, they might have already found your transcript on your LinkedIn profile and call you whilst you’re at work. The attacker poses as an administrator at your university wanting to make sure your records are up to date – they tell you what your name is and read you your student id number and then ask you to confirm your date of birth – in an act of building false trust.
The attacker then asks you to provide your address and current telephone number to ensure the university records are up to date – which you provide. The caller thanks you for your assistance, wishes you a good day and the call ends. The conversation goes to the back of your mind along with any other day to day calls that you don’t need to remember.
Cyber-attack
You might be asking yourself why an attacker would want to pretend to be you after you’ve already graduated – but universities do typically keep graduates accounts active for a set period of time after they’ve left the institution. This provides an avenue through which attackers could exploit the information they’ve found on social media and after obtaining further information from their target, to gain control of your university account.
Now that the fraudster has access to the information from your transcript as well as your address and contact number, they can now contact the University and pretend to be you.
Why is this important? Over the last few years, cyber-attacks against universities have been increasing as research data and personal data held by these institutions continually grows in size and value over time. Having access to your account, might help a social engineer to deploy malware or ransomware.
In 2019, the University of Maastricht was taken completely offline after attackers managed to deploy ransomware within their systems. Likewise, Brown University had to take systems offline in April this year following a cyber-attack and the University of Sunderland announced system outages in October this year following an attack.
Why should I care?
Depending on the experience you had whilst at university, you might not particularly care if your institution is attacked after your graduation – but the scenario above can also be applied in reverse. If you become the target rather than your institution, lets assume because an attacker is interested in targeting your graduate employer, the information you’ve shared on social media could be used to find out more about you by impersonating you when contacting your university.
In summary, graduating is for most students a once in a lifetime experience and it’s only natural to want to shout from the rooftops after all the work you’ve put in has finally paid off.
Just don’t celebrate by posting your degree certificate, one of your most important legal documents, on the internet.